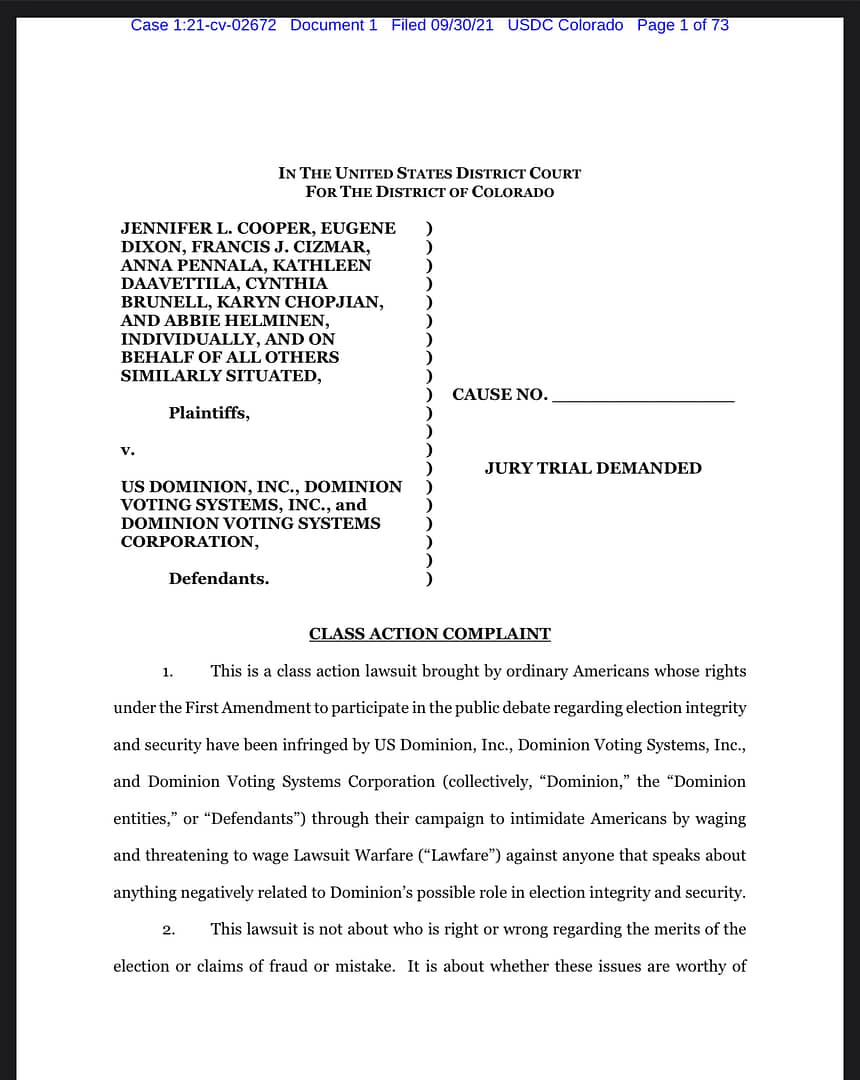
Trump Sues Clinton Cabal
President Trump filed lawsuit against the Clinton cabal, including the DNC, John Podesta, and many memorable associates.
Source: Trump Sues Clinton
Why the Unmasking of General Flynn Matters
In the frenzy of unmaskings by Obama administration officials in the waning days of his Presidency, the majority of those officials had no ‘need to know’ who the American citizen was on the call record in the NSA database. Neither was their unmasking the American citizen’s name for the purpose of creating an ‘intelligence product.’
While those are unusual and unwarranted acts, they are not, in and of themselves, illegal. What was illegal was leaking the American citizen’s name on that phone call to the media. That person’s name was classified.
The Obama administration sought out staff leakers and punished leakers more than any other in US history, according to the Washington Post, even to the point of using lie-detector tests on staff. The irony of the same administration accessing and leaking classified information to the media at the last moment is palpable.
The leak of General Flynn‘s name to friendly media outlets was strategically timed and to a certain effect: to poison the good name and reputation of a lifelong patriot who served America for 33 years in the US Army, and to set into motion the plan to overthrow the incoming President.
Once General Flynn’s name was published in obsequious media, connecting him with the Russians, and libeling him as a ‘Russian asset’ in Trump’s incoming administration, the stage was set. As one, on cue, worldwide media trumpeted the talking points that not only was Trump not fanatically against Russia, but he had advisors who were already plotting with Mr. Putin, to do what, none would say, but it had to be something nefarious.
The ‘Russian collusion’ narrative was promoted on every channel, on every show and on every newspaper’s pages. No where in the thousands of lines of text or hours of panel discussions was the fact that it was the unmasking and illegal leaking of an American citizen’s name done by people who absolutely knew the laws about classified information.
No mainstream journalist or reporter pointed out the illegality of that leak and the danger it posed to all American citizens with respect to our right to privacy and unreasonable search and seizure.
If a dedicated American Patriot like Gen. Michael Flynn could be unmasked and his name leaked to the media in order to destroy him, it could be done to any of us.
The danger of abuse of power like this, at the highest levels of American government cannot be overstated.
It is time for the American public to know the truth: who illegally leaked this name to the media. It is time for blind justice in this matter, for we cannot continue in a system where there are two sets of rules and laws are only applied to others.
United We Stand!!!
-
Any information and media you find on this site is free for you to use, and download. I encourage people to think for themselves. Please share the experience.
You can connect by Telegram at https://t.me/bakedcat
Chose Your Rabbit Hole
Bookmarks
- CIA's Use Of Journalists
- Europa: The Last Battle
- Jeffery Epstein Documents Released
- Judicial Watch
- Just The News
- Kate Hobbs – Sinaloa Cartel
- Key Pieces From The JFK Files
- Marco Polo Report On Hunter Bidens Laptop
- MG.Show
- National Archives
- Out of Shadows
- Project MKUltra
- Project Veritas Action
- Sara A Carter
- The Epoch Times
- US Department Of Justice
- WikiLeaks.org
- Zero Hedge
-
Recent Posts
- Hedgehog Collage 2 October 19, 2024
- Hedgehog Collage 1 October 4, 2024
- Viking Hedgehogs September 15, 2024
- Hedgewaffen September 8, 2024
- Erika! September 4, 2024
Meta